The design and implementation of bpftime
The hook implementation is based on binary rewriting and the underly technique is inspired by:
- Userspace function hook: frida-gum
- Syscall hooks: zpoline: a system call hook mechanism based on binary rewriting and pmem/syscall_intercept.
For more details about how to implement the inline hook, please refer to our blog: Implementing an Inline Hook in C in 5 minutes and the demo https://github.com/eunomia-bpf/inline-hook-demo
The injection of userspace eBPF runtime into a running program is based on ptrace and also provided by frida-gum library.
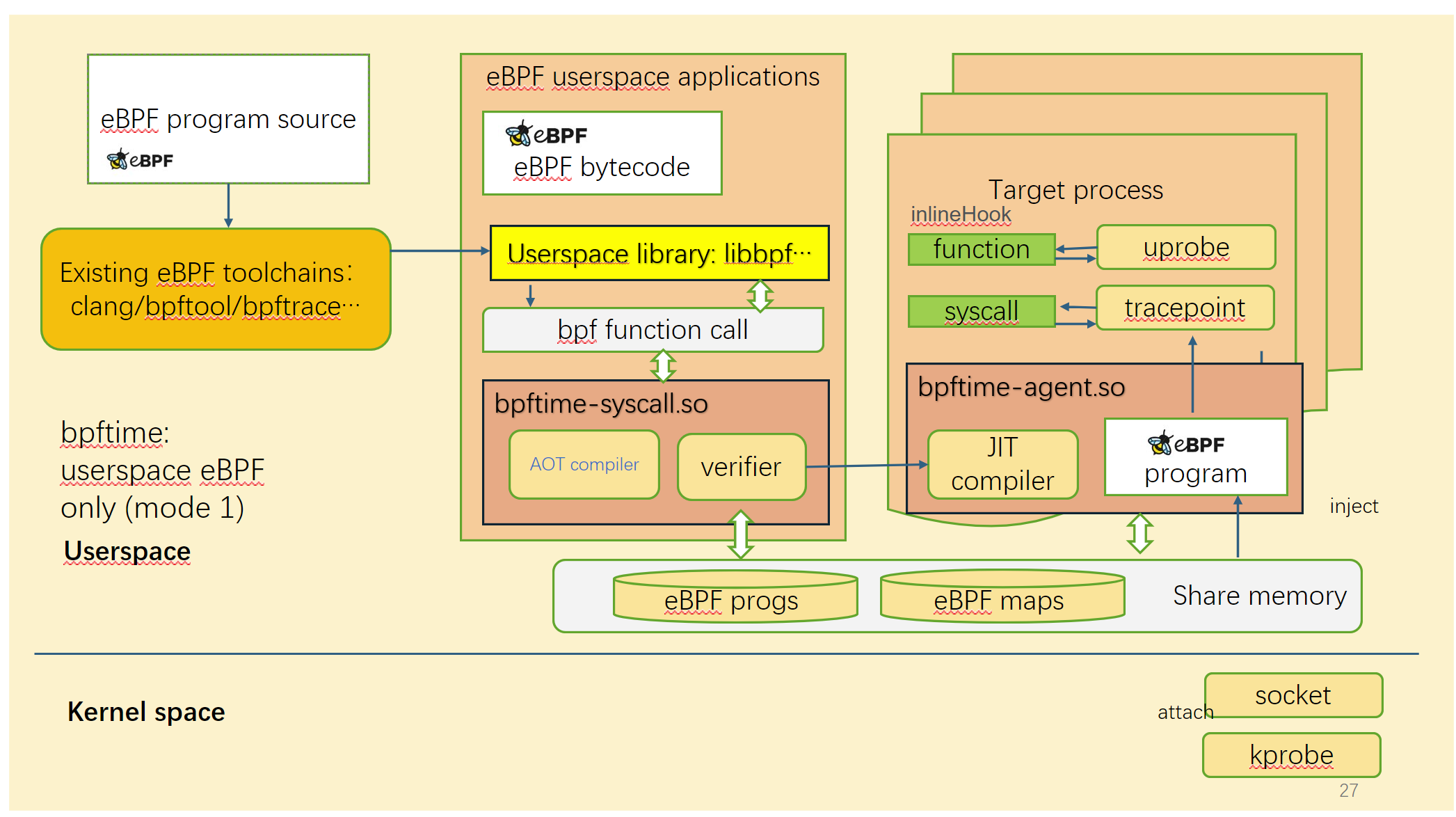
How the bpftime work entirely in userspace:
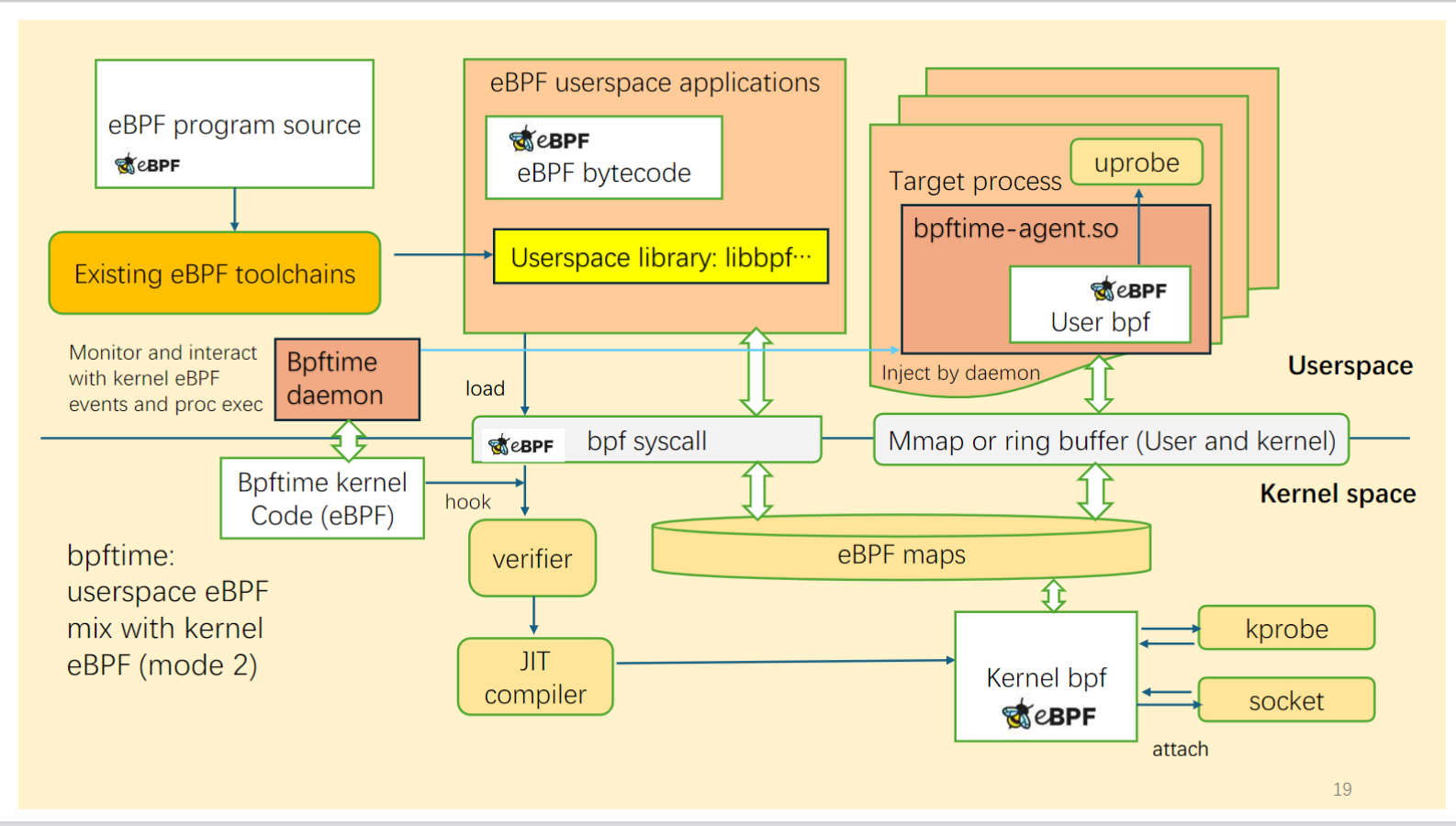
How the bpftime work with kernel eBPF:
For more details, please refer to: